Heat Maps are Just Bad Science
"They're all Ouija boards for conjuring the lowest common denominator of corporate groupthink." -- Richard Seiersen
Richard Seiersen, coauthor of the Cybercanon Hall of Fame book, “How to Measure Anything in Cybersecurity,” helped me set a new personal best at the Howard House Olympics in the early-morning-coffee spit take category. When I read the above LinkedIn quote earlier this summer, my distance not only exceeded my wife’s previous record but managed to hit the dog (Phoebe) on her way out of the room. Bonus! And, I love this Ouija Board image that he generated with some AI program. Richard is funny. But it makes me wonder about why the infosec profession is still using this tool (The Ouija Board like Heat Map) and it’s better looking sister, the Risk Register. Let’s find out.
What are Risk Registers and Heat Maps
According to Seiersen, “9 out of 10 enterprises use some form of risk registers and related risk art.” A Risk Register is usually some kind of spreadsheet that lists all the organization’s business risks along with some attributes that the leadership team considers important (likelihood, impact, owners, mitigation strategies, etc). It goes without saying that a cyber Risk Register is a subset of the business Risk Register that deals primarily with cyber risks.
Heat Maps are essentially bespoke spreadsheets that visualize the risk register to highlight the most serious risks. On the Y-axis, infosec professionals plot the likeliness of the risk happening. On the X-axis, they plot how impactful to the business the risk would be if it did happen. Naturally, the really nasty risks float high and to the right of the graph. The benign risks float low and to the left. Designers use the color “red” to designate the really scary risks, “yellow” for kind-of-scary risks, and “green” for not-that-scary risks. As you read from left to right, the graph gives the impression that the risks are heating up. That’s why they’re called Heat Maps.
Here’s the thing. For conveying risk to senior leadership, risk experts have demonstrated time and time again that Heat Maps are just bad science. On my Cybersecurity First Principles Book’s website, I included an appendix that lists many of the references (Look for “Research Summary on Why Heat Maps are Poor Vehicles for Conveying Risk”)
I want to be clear. Risk Registers are’nt bad science. They are basically checklists for things we have to monitor. For what they are, they are perfectly fine. But, when somebody has to summarize the Risk Register for senior leadership in order to explain the priorities and progress of the infosec team or to ask for resources to improve the organization’s security posture, Risk Registers don’t get the job done.
For example, a Risk Register that has more than, say, 50 entries, is tough to grok; especially if your a business leader and not a cybersecurity dork like me. To visually convey business risk to senior leaders in a way they could easily understand, infosec professionals turned to the Heat Map because they are visually compelling, not accurate in terms of risk forecasting, but they are great story aids if you’re trying to tell a Fear, Uncertainty, and Doubt (FUD) kind of story.
I’ve done this myself in my career; walked into the senior leadership meeting, showed the heat map, pointed to the really scary bits high and to the right on the chart, and declared that I needed a gazillion dollars to fix it. Sometimes that worked and sometimes it didn’t but it never gave the leadership team any sense of the real probability that something might happen and what it would cost the organization if it did. When I pulled the FUD card like that, I never gave the leadership team a chance to decide if the risk is within their own business tolerance. I just tried to scare the hell out of them.
Interestly, the research that proves Heat Maps are bad science has been around for more than a decade. How is it then that we are still using them? To answer that, we have to understand how Risk Registers and Heat Maps became part of the infosec culture.
Risk Register and Heat Map History
I didn’t discover a definitive source, but Abel Ndooka and Elgin Chetsanga (Herald Online - 2024) say that the concept of Risk Registers emerged as a formal practice sometime in the 1960s and 1970s. They were part of the evolving disciplines of project management and insurance. In the next decades (1970s and 1980s), Heat Maps started popping up as way to convey to senior leadership what the Risk Register meant.
According to Mary Levinson (My Management Guide - 2011) the UK’s Central Computer and Telecommunications Agency (CCTA) formally included “Risk Registers” in their PRINCE2 framework in 1996. PRINCE2 stands for Projects IN Controlled Environments, 2d edition, and is a methodology for improving and sustaining organizational performance. The impact to business leaders is that PRINCE2 made Risk Registers a thing you had to have for government compliance, at least in the UK.
For the security profession at large, according to Mike Gentile (LinkedIn 2018), the ISO Standards committee released the first version of ISO 27001: Information Security Management Systems (ISMS) in October 2005 and included Risk Registers as a requirement.
FYI: According to Will Kenton (Investopedia - 2010), the International Organization for Standardization (ISO) is a non-governmental group consisting of over 150 standards bodies from around the world. It was founded in 1947 and is headquartered in Geneva. Members participate in ISO’s governance, standards development, and strategic decision-making. There is one member per country and members can be full members with voting rights, correspondent members (observers), or subscriber members with more limited roles.
ISO 27001 put Risk Registers on the map for infosec professionals, which is not a bad thing, but because none of us had a better idea, we used Heat Maps to convey risk to the boss, which is.
What Visualization Tool Should We Use?
The visualization tool that we should replace Heat Maps with is the Loss Exceedance Curve (LEC). For anybody that has read my book, you know that I believe the absolute cybersecurity first principle is to reduce the probability of a material cyber event in the next business cycle. Risk forecasters use LECs to graphically show the probability that a specified level of financial loss will be exceeded within a given period. In terms of first principles, security leaders can forecast the probability of various dollar losses to their organization due to a cyber event. If they know the dollar amount that the company leadership thinks is material, they can absolutely calculate the probability of material loss to their organization.
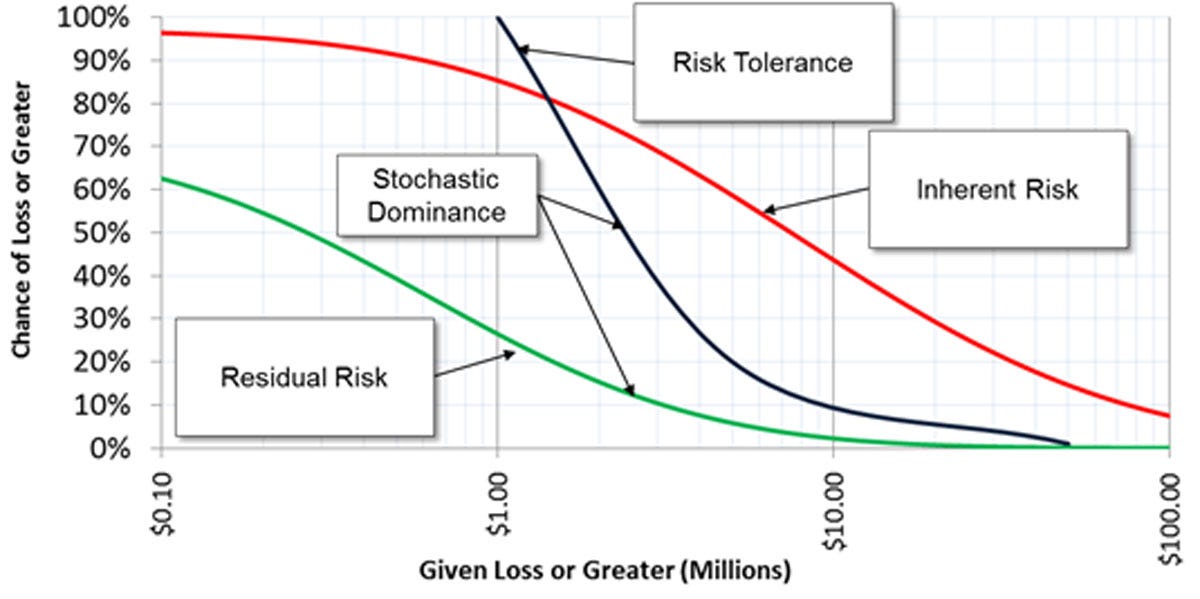
I cover risk forecasting, loss exceedance curves, and why reducing the probability of a material cyber event is the absolute first principle for every infosec program in chapter six of my book.
Take Away
The Risk Register is a useful tool to keep track of discovered risks to the business. It’s a practitioner’s tool, a day to day tool, and an ISO 27001 mandated tool. But the board doesn’t want to see your risk register. They may want to know if you have one, but they don’t want you to spend your 15 minutes twice a year in front of them walking them through it.
So, if you only have 15 minutes twice a year, what to present? Well, not the Ouija board that looks like a Heat Map. We have over a decade of science telling us that’s a bad idea. We need a replacement visualization tool that can convey the most important business information to senior leaders in a glance: what is the probability of a material cyber event? That tool is the Loss Exceedance Curve.
At some point in the future of this substack, I will walk you through how to do that. In the mean time, you can checkout Seiersen’s book and my book to get you started.
Source
Richard Seiersen, 2025. What are your thoughts on risk registers and matrices? [LinkedIn Post]. LinkedIn. URL https://www.linkedin.com/posts/richardseiersen_ciso-riskmanagement-crq-activity-7336775295619780610-7TsA/
Timeline: Risk Registers and Heat Maps
1873
The earliest known Heat Map example: “Toussaint Loua used a hand-drawn and colored shaded matrix to visualize social statistics across the districts of Paris.”
1960s- 1980s:
Risk Registers and Heat Maps become an accepted best practice for project management and insurance.
1996
The UK’s Central Computer and Telecommunications Agency (CCTA) formally includes “Risk Registers” in their PRINCE2 framework.
October 2005
The ISO Standards committee released the first version of ISO 27001: Information Security Management Systems (ISMS) in October 2005 and included Risk Registers as a requirement.
References
Abel Ndooka, Elgin Chetsanga, 2024. Are risk registers still relevant? [Analysis]. Herald Online. URL https://www.heraldonline.co.zw/are-risk-registers-still-relevant/
Bob Clark, Douglas Hubbard, Richard Seiersen , 2017. Author Interview: “How To Measure Anything in Cybersecurity Risk” - [WWW Document]. CyberCanon Gala - YouTube. URL
Douglas W. Hubbard, Richard Seiersen, 2023. How to Measure Anything in Cybersecurity Risk 2 Edition [Cybercanon Hall of Fame Book]. Goodreads. URL https://www.goodreads.com/book/show/78294350-how-to-measure-anything-in-cybersecurity-risk
Graeme Keith, 2025. The misery of matrices [Analysis]. LinkedIn. URL https://www.linkedin.com/pulse/misery-matrices-graeme-keith-nmktf/
Jeff Lowder, 2025. Still using heat maps to communicate cyber risk? [Explainer] LinkedIn. URL https://www.linkedin.com/posts/jlowder_informationrisk-quantitativeriskanalysis-activity-7340957633333366784-corc/
Mary Levinson, 2011. PRINCE2 Methodology: Definition, Purpose, Benefits [Explainer]. My Management Guide. URL https://mymanagementguide.com/prince2-methodology-overview-history-definition-meaning-benefits-certification/
Mike Gentile, 2018. Re-Inventing the Cyber Security Risk Register [Explainer]. LinkedIn. URL https://www.linkedin.com/pulse/re-inventing-cyber-security-risk-register-mike-gentile/
Rick Howard, 2025. A Metaphor for Conveying Risk [Explainer]. Rick’s First Principles Newsletter. URL https://diffuser.substack.com/p/a-metaphor-for-conveying-risk
Rick Howard, 2023. Cybersecurity First Principles: A Reboot of Strategy and Tactics [Book]. Amazon. URL https://www.amazon.com/Cybersecurity-First-Principles-Strategy-Tactics-ebook/dp/B0C35HQFC3/ref=sr_1_1
Rick Howard, 2023. Supporting Documents for Cybersecurity First Principles [Book Appendix]. Research Summary on Why Heat Maps are Poor Vehicles for Conveying Risk - The CyberWire. URL https://www.n2k.com/cybersecurityfirstprinciplesbook
Rick Howard, Steve Winterfeld, 2025. How to Measure Anything in Cybersecurity Risk [Hall of Fame Reviews]. CyberCanon. URL https://cybercanon.org/how-to-measure-anything-in-cybersecurity-risk/
Staff, 2021. The History of ISO 27001 [Explainer]. Secureframe. URL https://secureframe.com/hub/iso-27001/history
Staff, 2025. What Is PRINCE2? The Definition, History & Benefits [Explainer]. Prince2. URL https://www.prince2.com/usa/what-is-prince2
Will Kenton, 2010. What Is the International Organization for Standardization (ISO)? [Explainer]. Investopedia. URL https://www.investopedia.com/terms/i/international-organization-for-standardization-iso.asp
Wilkinson, L., Michael Friendly, 2012. The History of the Cluster Heat Map [Explainer]. The American Statistician - Pages 179-184 . URL https://www.tandfonline.com/doi/epdf/10.1198/tas.2009.0033






