The Kill Chain Rises from the Dead
ATT&CK v19, Tidal Cyber, and Anthropic’s Mythos may finally make intrusion kill chain prevention practical.
Like every good zombie in my favorite horror movies, intrusion kill chain prevention refuses to die.
In April, MITRE released ATT&CK v19. If one of your infosec strategies is Threat Led Defense (Intrusion Kill Chain Prevention) and your intelligence team is collecting and transforming raw information into intelligence products using some variation of the Diamond Model, then you’re probably already paying attention to this release.
In a previous essay, I explained how the Lockheed Martin Kill Chain paper, the Department of Defense Diamond Model paper, the MITRE ATT&CK framework, and Tidal Cyber’s Threat Led Defense are all related (See Sources: The Next Evolution for the Intrusion Kill Chain Prevention Strategy). Pertinent to this essay is that the ATT&CK framework is the industry’s free, open source, de facto standard for representing and sharing adversary playbook intelligence and MITRE just gave it an upgrade.
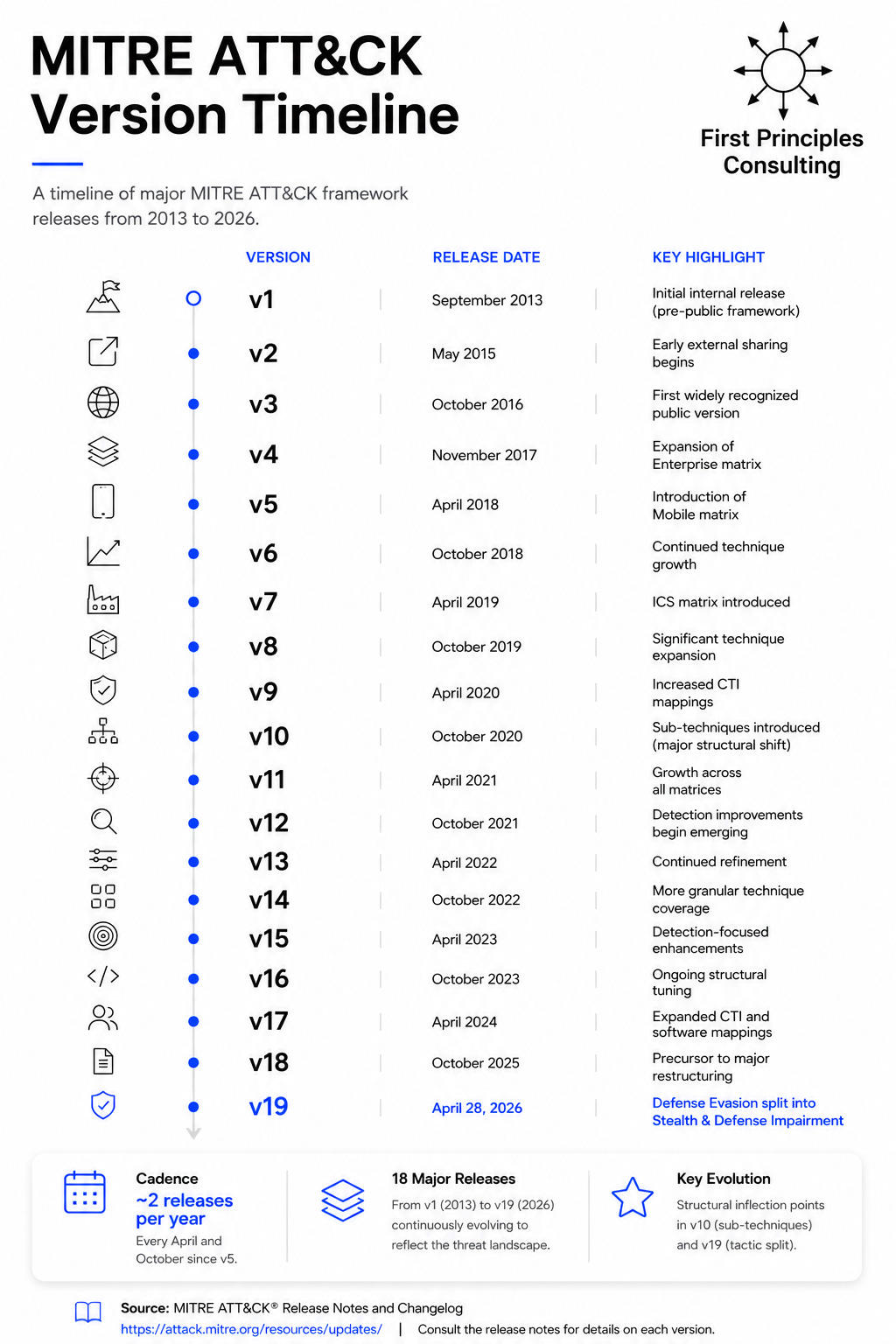
Their intelligence analysts have been releasing an upgrade roughly twice a year since version 1 in 2013 (See infographic at the bottom). In this latest version, arguably the most significant change is to the Defense Evasion tactic. Before I dive into the details of that, let me refresh you on the key components of the ATT&CK taxonomy.
The MITRE ATT&CK Taxonomy
Campaigns
When a hacker group conducts a coordinated operation against a set of victims in pursuit of a specific objective, MITRE ATT&CK calls that effort a campaign. A campaign is a coherent series of intrusion activities that occur over a defined period of time and share common objectives, infrastructure, or tradecraft.
The operational steps used during a campaign often resemble the phases described in the Lockheed Martin Cyber Kill Chain model: reconnaissance, initial access, execution, persistence, lateral movement, and actions on objectives.
A hacker group may reuse elements of a campaign against multiple victims while adapting tactics, techniques, infrastructure, and malware as the operation evolves.
Intrusion Sets
An intrusion set is the long-lived adversary organization or operational team responsible for conducting one or more campaigns over time. Cyber threat intelligence analysts assign names to these intrusion sets in order to track their behavior, infrastructure, and historical operations.
Examples include:
Charming Kitten: Iranian espionage-focused threat actor.
Wizard Spider: Criminal syndicate associated with Ryuk and TrickBot operations.
Volt Typhoon: Chinese attacks targeting critical infrastructure.
An intrusion set may conduct multiple campaigns with different objectives, victims, and operational playbooks.
For example, MITRE ATT&CK associates multiple campaigns with Charming Kitten, including:
Newscaster Campaign: Long-term social engineering and credential theft.
COVID/Medical Research Targeting: Espionage against healthcare and research organizations.
Recruiting-lure operations similar to “Operation Dream Job”: Human targeting and malware delivery.
In short, a campaign is a specific operation. An intrusion set is the adversary organization conducting multiple campaigns over time.
Tactics:
Each campaign or intrusion set will have multiple steps that the hacker group must execute. Broadly speaking, this is the hacker group’s intent at each phase of the intrusion kill chain.
Techniques
For each tactic, there are one or more general-purpose methods hacker groups use to pursue the tactic.
Sub-Techniques:
For each technique, there are one or more variants hacker groups use.
Procedures:
For each technique or sub-technique, intelligence analysts collect the actual observed hacker behavior on the victim’s systems.
Example
Campaign: KV Botnet Activity
Intrusion Set: Volt Typhoon
Kill Chain Phase: Actions on Objectives
Tactic: Defense Evasion
Technique: Command and Scripting Interpreter (T1059)
Sub-technique: PowerShell (T1059.001)
Procedure: Used native PowerShell commands and WMI to avoid dropping malware and blend into administrator activity
How Many Attack Campaigns in the World?
Specifically, at any given moment, how many distinct operational campaigns are simultaneously active across the internet?” The MITRE ATT&CK framework can’t answer that question. It’s not a live operational intelligence platform. It’s a curated historical knowledge base with manually modeled adversary behavior based on published reporting. It does not maintain real-time campaign counts, active operation telemetry, or continuously updated operational status. To find the number, we’re going to have to do some Fermi estimating.
The MITRE ATT&CK framework tracks roughly 190 different intrusion sets. Let’s assume that most have at least one campaign running at any given time and some might have two or three.
My best-order-of-magnitude estimate, based on the ATT&CK database, is that the range of active operational hacker campaigns running on the internet on any given day is between 500 and 1,000.
But, ATT&CK mostly tracks nation state activity with a handful of impactful cyber crime campaigns. If you include other security vendor’s estimates, like Microsoft , there are roughly 300 other unique cyber crime or hacktivist intrusion sets that run one or more campaigns. Combining the two, I will adjust my estimate upward. My new range is between 1,000 and 1,500 unique attack campaigns that are running on the internet for any given day.
That Seems Small
When asked the question, most infosec professionals think that range is too small. They usually estimate that the number has to be in the hundreds of thousands if not in the millions. The confusion stems from conflating the number of ongoing campaigns vs the number of targeted victims engaged in those campaigns.
Once a hacker team crafts a playbook that works in the wild, they don’t change it for every targeted victim. They just keep running the same playbook against multiple victims until some network defender forces them to stop. That means that the number of attacks in the wild could well be north of 100,000 if not a million. That’s why the problem feels so daunting.
But the actual number of distinct adversary playbooks running at any given moment, the playbook that we have to defend against, is only between 1,000 and 1,500. That’s the reason that threat led defense (intrusion kill chain prevention) is so compelling. It gives the network defender the advantage.
Threat Led Defense Gives the Defender the Advantage
Since there are only 1,500 adversary playbooks, it’s possible that we could deploy detection and prevention controls for every phase of the kill chain mapped to every tool in our security stack. These controls would be specific for every hacker campaign based on known TTPs.
Mature intrusion sets (like APT29, APT28, the Lazarus Group, and the Sandworm Team) contain between 20 and 60 steps (techniques) in their attack campaign. That means they have to string together a lot of things in order to complete their mission.
The beauty of the intrusion kill chain strategy (threat led defense) is that the network defender only has to prevent one of those techniques to defeat the attack; to break the attack chain. That’s what we mean with the phrase “The Kill Chain.” There are many places along the attack chain where the network defender can kill the attack. Even if the hacker group finds a work-around to our defensive measure at step 29, our prevention controls for steps 30-60 will kill the attack.
Hard to Do
In theory, this is a great approach. In practice though, it turns out that this is really hard to implement. It’s also quite expensive. Only large organizations with big intelligence teams and lots of money can afford it.
And, until recently, creating detection and prevention controls for every tool in your security stack mapped to MITRE’s TTPs hasn’t been that easy. Tactics, techniques, and sub-techniques are too generic in most cases to develop a meaningful prevention control. I mean, what firewall rule do you write to handle the following?
Tactic: Defense Evasion
Technique: Command and Scripting Interpreter (T1059)
Sub-technique: PowerShell (T1059.001)
Those are just framing categories. What network defenders need are details on procedures, the third leg of the MITRE TTP triad.
Hope: Intrusion Kill Chain Prevention Strategy Rising from the Grave
Until recently, the MITRE ATT&CK framework has been light on documented procedures. It has been tough to get them from public reporting. They exist, but they are rare.
Last year, Tidal Cyber (a startup I advise), pointed their large language model at public intelligence reports looking for procedures. They have been wildly successful. In a short amount of time, they have collected some 20,000 procedure examples and shared them with the community via the ATT&CK framework and their own platform. It’s a game changer.
But, converting public reporting intelligence reports into prevention controls has, up until now, been mostly manual. Automating that task has always been in the “too hard to do” bucket. Network defenders were always afraid that they might break some material business process as a secondary effect. That means that transforming these relatively new 20,000 procedure examples into prevention controls are out of reach for most organizations. They don’t have the resources to manually go through the list.
Counterintuitively, the hope comes with Anthropic’s release of Mythos a few weeks ago; the AI tool designed to automatically discover software vulnerabilities and write exploit code to leverage them. Boards and infosec professionals have started to realize that automating responses to new threats like emerging exploit code might add enterprise risk by sometimes breaking things, but it may be the only way to prevent a catastrophic cyber event in the future. It’s the same idea for automating prevention control deployments based on procedures.
And, by the way, using AI tools goes both ways. If hackers can use AI to rapidly develop new exploit code, network defenders can use those same tools to automate their defensive response.
A year ago, if asked, I would have told you that threat led defense, the intrusion kill chain prevention strategy from my Cybersecurity First Principles book, is a failed strategy for most organizations.
If you’re a Fortune 500 company, you can afford it. But the strategy is out of reach for most organizations. It’s the right idea but is too hard to implement. It can’t be a first principle strategy if it doesn’t apply to everybody.
Today though, with the advent of Tidal Cyber’s ability to automatically cull meaningful procedures from public intelligence reporting, and Mythos showing business leadership that reactive automation is the way to go, the strategy has gained new energy.
And that’s why I’m excited about the ATT&CK ver 19. It demonstrates that the strategy is evolving, changing as we learn how to do it better. In version 19, MITRE has decided to split the Defense Evasion tactic.
The Defense Evasion Split
According to MITRE’s Allison Henao and Alice Koeninger, the Defense Evasion tactic had become a placeholder.
With over 40 techniques under a single umbrella, Defense Evasion became something of a catch-all. A behavior landed there if it was evasion-adjacent, regardless of what the adversary was actually doing.
These techniques went back and forth between hacker groups trying to hide their presence (stealth) by making everything look normal and hacker groups actively taking over infrastructure so that they won’t get noticed (Impair Defenses). Clearly, those two sets of activities are not the same and require different responses.
To address the problem, MITRE has effectively retired the Defense Evasion tactic and replaced it with two separate tactics: Stealth and Impair Defenses.
Take away
I used to think intrusion kill chain prevention was strategically correct but operationally unrealistic. The theory was elegant. The implementation was brutal. Too much manual effort. Too much intelligence work. Too much tuning. Too many opportunities to break production systems. But AI changes the economics. Suddenly, collecting procedures at scale is possible. Mapping them to controls is possible. Automating defensive response is becoming possible. We may finally be approaching the moment where defenders can fight at machine speed without completely surrendering control to the machines. That’s why ATT&CK v19 matters. It’s not just another framework update. It’s evidence that the defensive model itself is evolving.
Note on the Infographic: This is my best guess reading through the MITRE documentation. If there are errors, that’s on me. If you find any, let me know. MITRE didn’t start officially versioning the framework until 2018. Prior, they just added new features to the website. I tried to capture the significant changes since the beginning.
Source
Amy L. Robertson, 2026. ATT&CK v19: The Defense Evasion Split, ICS Sub-Techniques, New AI & Social Engineering Coverage, and Detection Strategies for Mobile [Explainer]. MITRE ATT&CK® on Medium, URL: https://medium.com/mitre-attack/attack-v19-ff329cb65d66
References
Blake E. Strom, Andy Applebaum, Doug P. Miller, Kathryn C. Nickels, Adam G. Pennington, Cody B. Thomas, 2018. MITRE ATT&CKTM: Design and Philosophy [Paper]. MITRE. URL https://www.mitre.org/sites/default/files/publications/pr-18-0944-11-mitre-attack-design-and-philosophy.pdf
Eric Hutchins, Michael Cloppert, Rohan Amin, 2010. Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains [Paper]. Lockheed Martin Corporation. URL https://www.lockheedmartin.com/content/dam/lockheed-martin/rms/documents/cyber/LM-White-Paper-Intel-Driven-Defense.pdf
Jonathan Nunez, Carlos De Sola Caraballo, Jaime Anderson, 2026. Magic Quadrant for Cyberthreat Intelligence Technologies [Report]. Gartner, URL: https://www.gartner.com/doc/reprints?id=1-2NB75Z8E&ct=260505&st=sb
Lauren Lusty, Allison Henao, Alice Koeninger, 2026. Defense Evasion Split: A Tale of Two Tactics [Explainer]. MITRE ATT&CK® on Medium, URL: https://medium.com/mitre-attack/defense-evasion-split-5d533545fa32
Rick Howard, 2022. Kill chain trifecta: Lockheed Martin, ATT&CK, and Diamond. [Analysis]. The CyberWire. URL https://thecyberwire.com/podcasts/cso-perspectives/72/notes
Rick Howard, 2023. Cybersecurity First Principles: A Reboot of Strategy and Tactics [A 2026 Canon Hall of Fame Book]. Amazon. URL https://www.amazon.com/Cybersecurity-First-Principles-Strategy-Tactics-ebook/dp/B0C35HQFC3/ref=sr_1_1
Rick Howard, Blake Strom, 2023. MITRE ATT&CK Framework [Podcast]. The CyberWire. URL https://thecyberwire.com/podcasts/daily-podcast/1968/transcript
Rick Howard, 2025. The Next Evolution for the Intrusion Kill Chain Prevention Strategy [Explainer]. Rick’s First Principles Newsletter (Substack), URL: https://diffuser.substack.com/p/the-next-evolution-for-the-intrusion
Sergio Caltagirone, Andrew Pendergast, Christopher Betz, 2011. The Diamond Model of Intrusion Analysis. Center for Cyber Threat Intelligence and Threat Research [Paper]. https://www.activeresponse.org/. URL https://www.activeresponse.org/wp-content/uploads/2013/07/diamond.pdf
Staff, 2024. Microsoft Digital Defense Report 2024 [Open Source Intelligence Report]. Microsoft Security Insider, URL: https://www.microsoft.com/en-us/security/security-insider/threat-landscape/microsoft-digital-defense-report-2024
Staff, 28 April 2026. Updates: MITRE ATT&CK 19 [Announcement]. MITRE ATT&CK, URL: https://attack.mitre.org/resources/updates/