Thoughts on The Cuckoo's Egg
Is this classic book still relevant today?
Hot Take
This book is likely the first public account of a cyber espionage campaign, orchestrated by the Russians in the late 1980s, leveraging German hacker mercenaries, to infiltrate U.S. academic institutions as a pathway into U.S. government systems. It’s the book that launched many a cybersecurity career for practitioners of a certain age (Read that as “old as dirt.”)
That said, I think it might be time to move this classic from the must-read pile to the historical-archive pile.
My History
I first read this book back in 1989 when I was in grad school. The U.S. Army sent me to the Naval Postgraduate School to get educated on how to become an Army automator. Read that last sentence again and you will get the flavor of Army thinking at the time (Navy school → Army Automator. Hey, don’t ask me. I just worked there.)
Instead of working on my graduate thesis (which I was far behind on), I devoured this book over a weekend. It was a revelation. For me, and many of my peers both in the service and out, this book created the path to a cybersecurity profession. It showed that cybersecurity could be a career.
For the next 30 years
Stoll’s book was the first thing I handed to newbies when they came to work for me. I recommended it whenever anybody asked me how to break into the field. It was one of the first books I reviewed when I started the Cybersecurity Canon Project many years ago.
And it was one of the first books that the Cybersecurity Canon committee inducted into the Hall of Fame back in 2016 along with Kim Zetter’s Countdown to Zero Day and Brian Krebs’ Spam Nation.
But, a couple of weeks ago, the Cybersecurity Canon Project and the Cyber Guild selected this book for our joint quarterly discussion. This group of about 30 northern virginia-cybersecurity-nerds meets regularly to talk about Canon Hall of Fame titles. I’m the facilitator, but I was a bit concerned. After all, the book is nearly 40 years old. I wondered whether it would still resonate. Would younger readers still see it as an inspiration even though it takes place in a world where
Nobody had direct Internet access at home.
CompuServe was a primary gateway to being online.
AOL didn’t become a thing until 1993.
The web browser didn’t exist either.
NCSA Mosaic didn’t show up until 1993.
Cell phones were the size of bowling balls.
Most home computers ran DOS on IBM PCs (or clones).
Macs were for the cool kids, but they were niche.
Unix powered the serious university and government computers, but those systems were far removed from anything ordinary users ever experienced.
Still, Dr. Stoll did invent incident response. Despite the new tooling available today, his method is largely unchanged. And we still haven’t solved the problem of information sharing with the government (something that Stoll complained about for the entire book). And the weakness that the German hackers leveraged across the U.S. networks was the inability of users to pick good passwords. Remarkably, this remains a problem some 60 years after Dr. Fernando Corbató introduced computer passwords at MIT.
The question is, do those facts make the book a must-read in 2026?
I don’t think so.
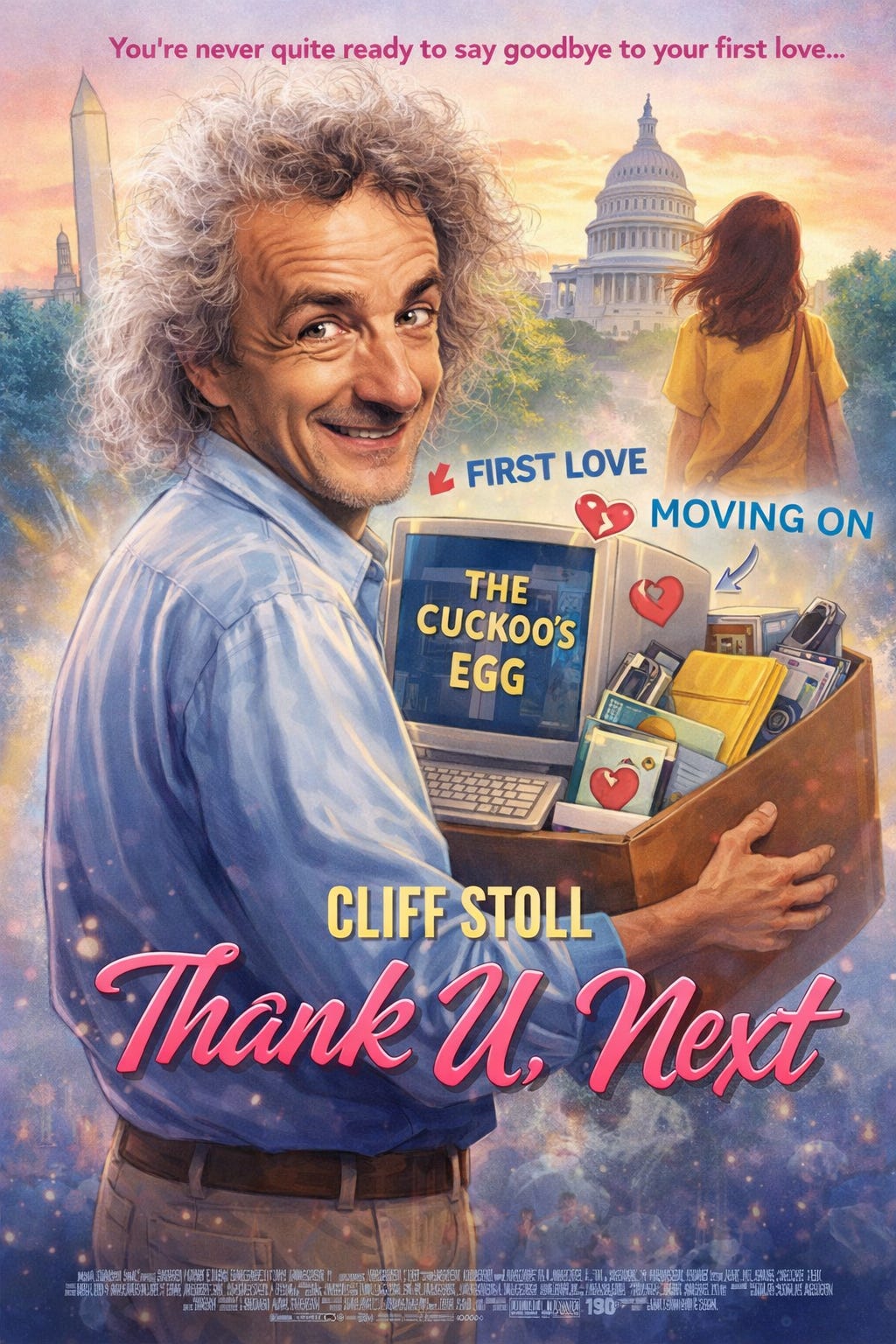
My First Love
Stoll’s “Cuckoo’s Egg” was my first love in the technology space. And it’s tough to let go of something that powerful. The thing that sealed the deal for me, the thing that cemented my love affair with it, was after I finished the book. I immediately wrote a gushing email to the author proclaiming that the book completely changed my view of the world. Back then, email was so new that authors put their real email addresses into their books. Dr. Stoll answered me in 15 minutes. That was it. I was hooked.
But, as much as I hate to admit it, even with an incipient love letter chain started, I think it’s time to make a clean break. Like the Ariana Grande song says: “thank you, next.” Cuckoo’s Egg shaped how I see the world. But after 40 years, it’s time to move on.
Source
Clifford Stoll, 1989. The Cuckoo’s Egg: Tracking a Spy Through the Maze of Computer Espionage [2016 Canon Hall of Fame Book].
Goodreads. URL https://www.goodreads.com/book/show/18154.The_Cuckoo_s_Egg
Cybersecurity Canon Review: https://cybercanon.org/the-cuckoos-egg/
Buy URL: https://amzn.to/3JWAhsb
Reference
Brian Krebs, 2014. Spam Nation: The Inside Story of Organized Cybercrime — from Global Epidemic to Your Front Door [2016 Canon Hall of Fame Book].
Goodreads URL: https://www.goodreads.com/book/show/18509663-spam-nation
Canon URL: https://cybercanon.org/spam-nation/
Buy URL: https://amzn.to/4o0m5wz
Clifford Stoll, 1988. STALKING THE WILY HACKER [Journal Article]. COMMUNICATION OF THE ACM, vol. 31. No. 5. URL http://pdf.textfiles.com/academics/wilyhacker.pdf
Clifford Stoll, 1996. Second Thoughts on the Information Highway [Presentation]. C-SPAN. URL https://www.c-span.org/program/public-affairs-event/second-thoughts-on-the-information-highway/132866
Clifford Stoll, 1999. High Tech Heretic [Book Discussion. C-SPAN. URL https://www.c-span.org/program/book-tv/high-tech-heretic/133700
Clifford Stoll, Brian Lamb, 1996. Cuckoo’s Egg Discussion [Author Interview]. C-SPAN. URL https://www.c-span.org/program/public-affairs-event/second-thoughts-on-the-information-highway/132866
Clifford Stoll, 2008. Clifford Stoll: Astronomer, educator, skeptic [Bio]. TED Talks. URL https://www.ted.com/speakers/clifford_stoll
Clifford Stoll, 2008. The call to learn [Ted Talk]. TED. URL https://www.ted.com/talks/clifford_stoll_the_call_to_learn
Clifford Stoll, n.d. Acme Klein Bottle [Company Web Page]. URL https://www.kleinbottle.com/
Clifford Stoll, n.d. Why read The Cuckoo’s Egg? [Book Explainer]. Book DNA. URL https://bookdna.com/book/the-cuckoos-egg
David Kahn, 1967. The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet [Book]. Goodreads. URL https://www.goodreads.com/book/show/29608.The_Codebreakers
James Bamford, 1982. The Puzzle Palace: Inside the National Security Agency, America’s Most Secret Intelligence Organization [Book]. Goodreads. URL https://www.goodreads.com/book/show/804860.The_Puzzle_Palace
John Markoff, 1989. West Germans Raid Spy Ring That Violated U.S. Computers [News]. The New York Times. URL https://www.nytimes.com/1989/03/03/world/west-germans-raid-spy-ring-that-violated-us-computers.html
Kim Zetter, 2014. Countdown to Zero Day: Stuxnet and the Launch of the World’s First Digital Weapon [2016 Canon Hall of Fame Book].
Goodreads URL: https://www.goodreads.com/book/show/18465875-countdown-to-zero-day
Canon Review URL: https://cybercanon.org/countdown-to-zero-day-stuxnet-and-the-launch-of-the-worlds-first-digital-weapon/
Amazon Buy URL: https://amzn.to/3JVc99m
Staff, n.d. GNU Emacs [Product Page. GNU Project. URL https://www.gnu.org/software/emacs/
Staff, n.d. The 1988 Morris worm, the internet’s first cyberattack [History]. Lawrence Livermore National Laboratory. URL https://st.llnl.gov/news/look-back/1988-morris-worm-internets-first-cyberattack
William E. Burrows, 1986. Deep Black: Space Espionage and National Security [Book]. Goodreads. URL https://www.goodreads.com/book/show/887319.Deep_Black
Ariana Grande, 2018. thank u, next (Official Video) [Music Video] YouTube
Cliff Stoll, 2013. The KGB, the Computer, and Me. [WWW Document]. NOVA - YouTube. URL
Clifford Stoll, 2017. Secrets to measuring a piece of paper [Explainer]. Numberphile - YouTube. URL